ZSipOs-Box
Make calls without uninvited listeners
Nowadays, there is a high probability that phone calls are being tapped. And this could lead to the
loss of
- trade secrets
- a competitive edge
- the development lead
- of contracts.
With ever more powerful computer chips and increasingly sophisticated software, it is also becoming easier to introduce security vulnerabilities and eavesdropping interfaces.
How can this be prevented?
By using a ZSipOs Box, which encrypts phone calls to make them tap-proof.
Why tap-proof?
All hardware and software modules in the box are open source. In particular, no proprietary CPU is used, in which the program code is not visible and may contain ‘backdoors’ or Trojans.
What does Open Source mean?
Both the software code and the programmes embedded in the components are freely accessible and verifiable. Any compromise of the code would therefore be public knowledge and would have no chance of success.
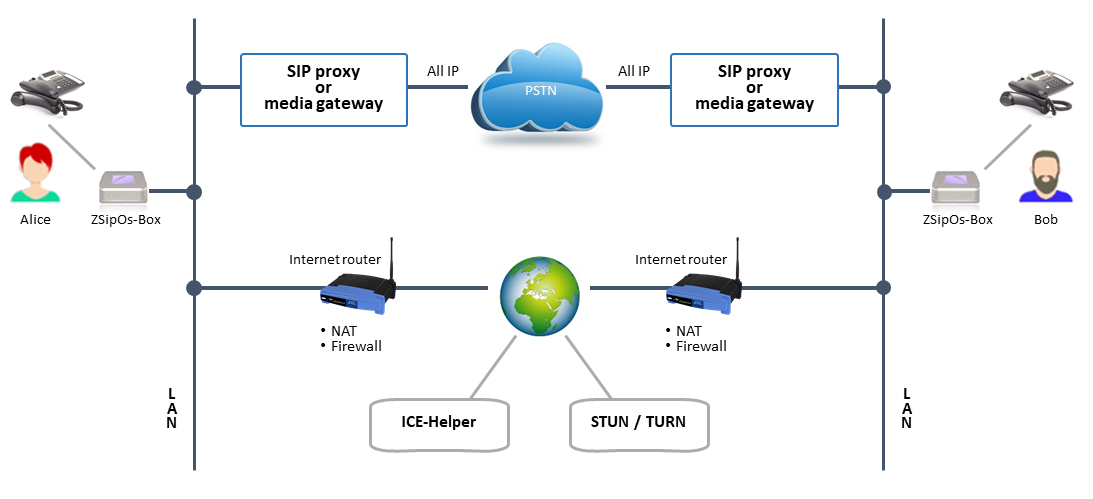
How does it work?
You will also need a compatible ZSipOs box at the other end of the line. Simply plug the box in between the IP phone and the network socket. To dial and make calls, use your phone as usual (pick up, dial, speak, hang up). Once the initial connection to the box has been established, a ‘fingerprint’ is generated, transmitted to your conversation partner’s box at the other end of the line, and displayed on the screens of both boxes. You then verbally verify the displayed ‘fingerprint’ with your conversation partner to confirm identity. If the numerical code matches, you have a guaranteed tap-proof telephone connection. The “fingerprint” is now stored in the box’s memory and no longer needs to be verified in future.
From now on, every call with this contact can only be encrypted by activating the box (pressing the button).
Conference calls
Provided that each participant has a User Box connected to their telephone, you can now hold tap-proof telephone conferences.
This project was funded by the NGI0 PET project, a fund established by NLnet foundation with financial support from the European Commission’s Next Generation Internet programme, uunder the auspices of the Directorate-General for Communications Networks, Content and Technology pursuant to Grant Agreement No 825310.